
iForensics: Forensic Services
Forensic Services
Digital Evidence: The Key to Uncovering the Truth
Are you facing the following challenges?
- Data deleted, hard drive damaged, and crucial files cannot be recovered?
- Encountered a cyber attack or data breach, and urgently need cybersecurity investigation and analysis?
- Intellectual property disputes or trade secrets leakage, but unable to obtain valid digital evidence?
- Facing cryptocurrency fraud, and unable to trace the flow of funds?
iForensics Digital Inc. focuses on providing comprehensive digital forensics services, covering intellectual property disputes, criminal pre-investigation operations, civil cases, and other investigation needs. We apply cutting-edge technologies and international standards to assist you in quickly solving problems, restoring data truths, from data recovery to virtual currency fund flow tracing, and from digital evidence analysis to courtroom support.
Service Process
Transparent and Efficient, Restoring Every Piece of Truth
Our forensic services follow a structured process, starting with in-depth needs interviews
to
fully
understand case details.
Based on your requirements, we tailor professional solutions to
ensure
services are both efficient and precise.

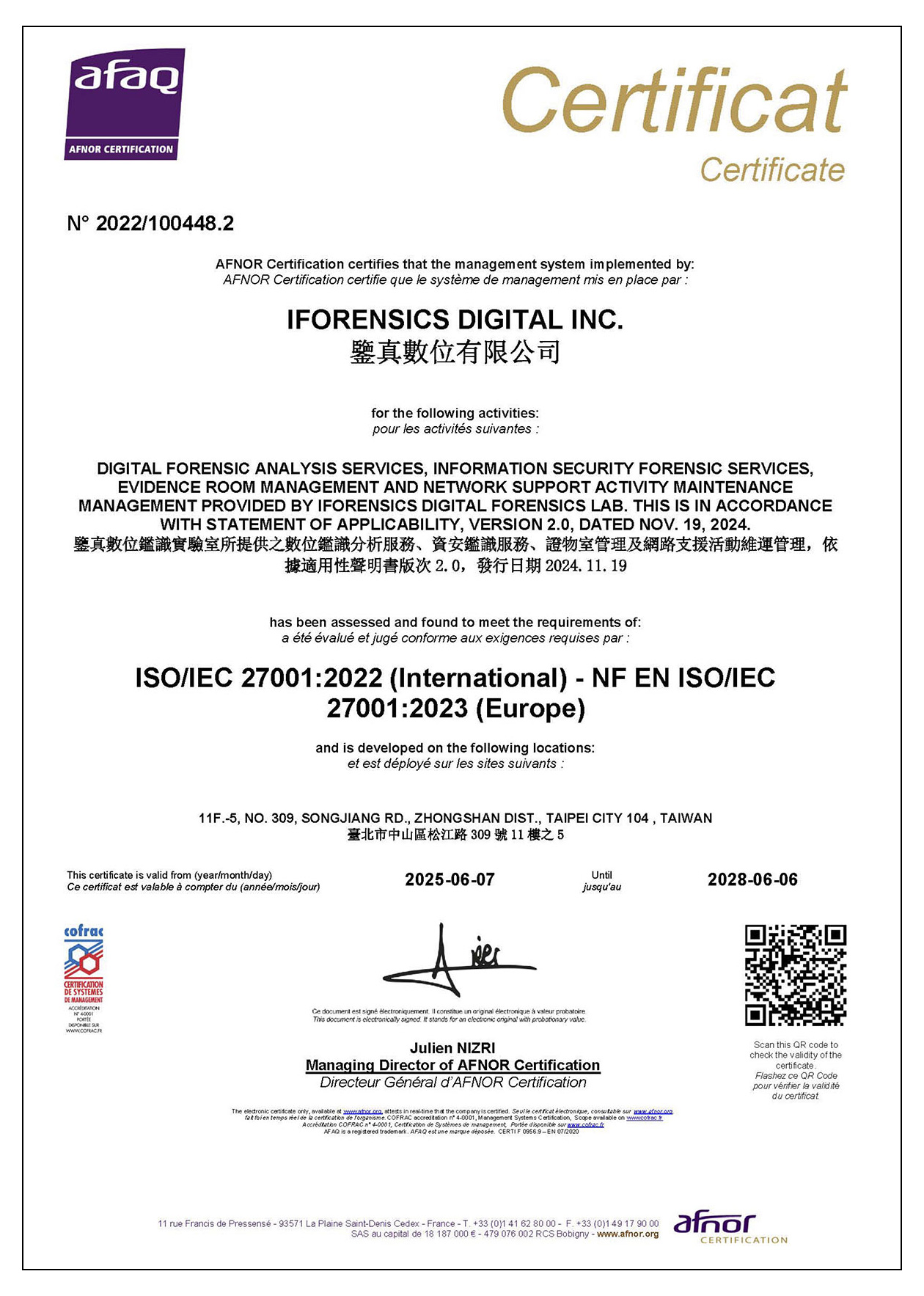
International Certifications
Dual Assurance in Laboratories and Information Security
ISO / IEC 17025:
Global accreditation for testing and calibration laboratories, validating iForensics
Digital
Inc.'s forensic laboratory for its excellence in technical precision and management
standards, ensuring clients receive accurate and reliable forensic reports.

ISO / IEC 27001:
International certification for Information Security Management Systems, ensuring
high
security and confidentiality in data processing and storage.
Digital Forensics and Information Security Certifications
The Best Proof of Professional Capability
Our team members hold numerous international digital forensics and information security
certifications,
providing higher-level protection and solutions for your cases.
Digital Forensics Professional Certifications:
EnCE、MCFE、MCME、ACE、BelkaCE、CHFI

Information Security Professional Certifications:
CISSP、CISA、CEH、ECIH、CPENT、ISO 27001 Lead Auditor、LPT

